3.3 Security Considerations
Although the differences between tethered and untethered are few, they are significant. For example, everyone has heard of the archetypal "black-hat packet sniffer," a giggling sociopath sitting on your physical Ethernet segment, surreptitiously logging packets for his own nefarious ends. This could be a disgruntled worker, a consultant with a bad attitude, or even (in one legendary case) a competitor with a laptop, time on his hands, and a lot of nerve.[1] Although switched networks, a reasonable working environment, and conscientious reception staff can go a long way to minimize exposure to the physical wiretapper, the stakes are raised with wireless. Suddenly, one no longer needs physical presence to log data: why bother trying to smuggle equipment onsite when you can crack from your own home or office two blocks away with a high-gain antenna?
As the story goes, a major computer hardware manufacturer once found a new "employee" sitting in a previously unoccupied cube. He had evidently been there for three weeks, plugged into the corporate network and happily logging data before HR got around to asking who he was.
Visions of cigarette smoking, pale skinned über-crackers in darkened rooms aside, there is a point that many admins tend to overlook when designing networks: the whole reason that the network exists is to connect people to each other! Services that are difficult for people to use will simply go unused. You may very well have the most cryptographically sound method on the planet for authenticating a user to the system. You may even have the latest in biometric identification, full winnow and chaff capability, and independently verified and digitally signed content assurance for every individual packet. But if the average user can't simply check her email, it's all for naught. If the road to hell is paved with good intentions, the customs checkpoint must certainly be run by the Overzealous Security Consultant.
The two primary concerns when dealing with wireless clients are these:
• Who is allowed to access network services?
• What services can authorized users access?
As it turns out, with a little planning, these problems can be addressed (or neatly sidestepped) in most real-world cases. In this section, we'll look at ways of designing a network that keeps your data flowing to where it belongs, as quickly and efficiently as possible.
Let's take a look at the tools we have available to put controls on who can access what.
3.3.1 WEP
The 802.11b specification outlines a form of encryption called wired equivalency privacy, or WEP. By encrypting packets at the MAC layer, only clients who know the "secret key" can associate with an access point or peer-to- peer group. Anyone without the key may be able to see network traffic, but every packet is encrypted.
The specification employs a 40-bit, shared-key RC4 PRNG[2] algorithm from RSA Data Security. Most cards that talk 802.11b (Agere Orinoco, Cisco Aironet, and Linksys WPC11, to name a few) support this encryption standard.
Pseudo-Random Number Generator. It could be worse, but entropy takes time.
Although hardware encryption sounds like a good idea, the implementation in 802.11b is far from perfect. First of all, the encryption happens at the link layer, not at the application layer. This means your communications are protected up to the gateway, but no further. Once it hits the wire, your packets are sent in the clear. Worse than that, every other legitimate wireless client who has the key can read your packets with impunity, since the key is shared across all clients. You can try it yourself; simply run tcpdump on your laptop and watch your neighbor's packets just fly by, even with WEP enabled.
Some manufacturers (e.g., Agere and Cisco) have implemented their own proprietary extensions to WEP, including 128-bit keys and dynamic key management. Unfortunately, because they are not defined by the 802.11b standard, there is no guarantee that cards from different manufacturers that use these extensions will interoperate (and, generally speaking, they don't).
To throw more kerosene on the burning WEP tire mound, a team of cryptographers at the University of California at Berkeley have identified weaknesses in the way WEP is implemented, effectively making the strength of encryption irrelevant. With all of these problems, why is WEP still supported by manufacturers? And what good is it for building public access networks?
WEP was not designed to be the ultimate "killer" security tool (nor can anything seriously claim to be). Its acronym makes the intention clear: wired equivalency privacy. In other words, the aim behind WEP was to provide no greater protection than you would have when you physically plug into your Ethernet network. (Keep in mind that in a wired Ethernet setting, there is no encryption provided by the protocol at all. That is what application layer security is for; see the tunneling discussion later in this chapter.)
What WEP does provide is an easy, generally effective, interoperable deterrent to unauthorized access. While it is technically feasible for a determined intruder to gain access, it is not only beyond the ability of most users, but usually not worth the time and effort, particularly if you are already giving away public network access!
As we'll see in Chapter 7, one area where WEP is particularly useful is at either end of a long point-to-point backbone link. In this application, unwanted clients could potentially degrade network performance for a large group of people, and WEP can help not only discourage would-be link thieves, but also encourage them to set up more public access gateways.
3.3.2 Routing and Firewalling
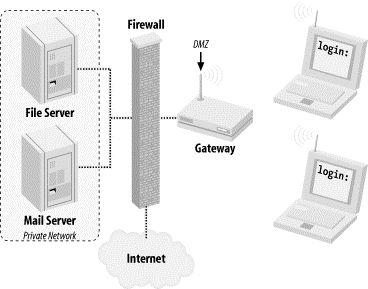
The primary security consideration for wireless network access is where to fit it into your existing network. Regardless of your gateway method (AP or DIY) you need to consider what services you want your wireless users to be able to access. Since the primary goal of this book is to describe methods for providing public access to network services (including access to the Internet), I strongly recommend setting up your wireless gateways in the same place you would any public resource: in your network's DMZ or outside your firewall altogether. That way, even in a complete breakdown of security precautions, the worst that any social deviant will end up with is Internet access, and not unrestricted access to your private internal network.
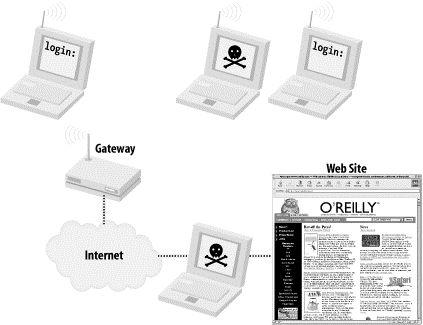
This configuration, as shown in Figure 3-5, leaves virtually no incentive for anyone to try to compromise your gateway, as the only thing to be gained would be greater Internet access. Attacks coming from the wireless interface can easily log MAC address and signal strength information. In IBSS mode, this is an even greater deterrent. As the would-be attacker needs to transmit to carry out an attack, they give away not only a unique identifier (their MAC address), but also their physical location!
Figure 3-5. Place your wireless gateways outside of your private network!
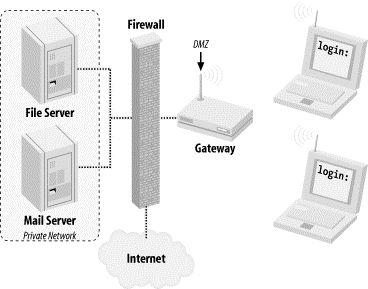
Assuming that all wireless connectivity takes place outside of your private network, what happens when you or your friends want to connect from the wireless back to the inside network? Won't other wireless users be able to just monitor your traffic and grab passwords and other sensitive information? Section 3.3.3 addresses this potential problem.
3.3.3 Encrypted Tunnels
Application layer encryption is a critical technology when dealing with untrusted networks (like public-access wireless links, for example). When using an encrypting tunnel, you can secure your communications from eavesdroppers all the way to the other end of the tunnel.
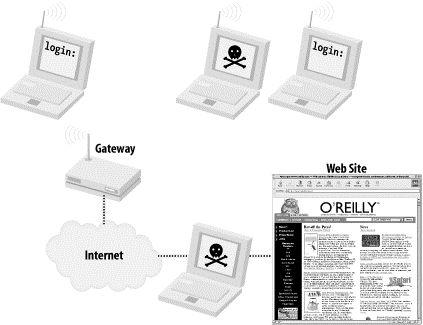
If you're using a tunnel from your laptop to another server, would-be black hats listening to your conversation will have the insurmountable task of cracking strong cryptography. Until someone finds a cheap way to build a quantum computer (and perhaps a cold fusion cell to power it), this activity is generally considered a waste of time. In Figure 3-6, a web server providing 128-bit SSL connections provides plenty of protection, all the way to your wireless laptop. SSL provides application layer encryption.
Figure 3-6. WEP only encrypts to the gateway, exposing your traffic to other wireless users and anything after the wire. Tunnels protect your traffic from end to end
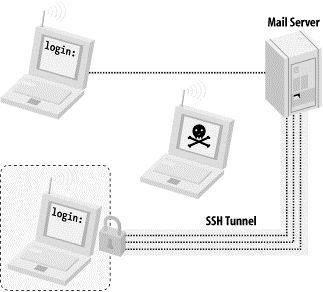
SSL is great for securing web traffic, but what about other network services? Take this typical scenario: You're at work or at home, merrily typing away on your wireless laptop. You want to retrieve your email from a mail server with a POP client (Netscape Mail, Eudora, fetchmail, etc.). If you connect to the machine directly, your email client sends your login and password "in the clear." This means that a nefarious individual somewhere between you and your mail server (either elsewhere on your wireless network, or even "on the wire" if you are separated by another network) could be listening and could grab a copy of your information en route. This login could then not only be used to gain unauthorized access to your email, but in many cases also to grant a shell account on your mail server!
To prevent this, you can use the tunneling capabilities of SSH. An SSH tunnel works like this: rather than connecting to the mail server directly, we first establish an SSH connection to the internal network that the mail server lives in (in this case, the wireless gateway). Your SSH client software sets up a port-forwarding mechanism, so that traffic that goes to your laptop's POP port magically gets forwarded over the encrypted tunnel and ends up at the mail server's POP port. You then point your email client to your local POP port, and it thinks it is talking to the remote end (only this time, the entire session is encrypted). Figure 3-7 shows a model of an SSH tunnel in a wireless network.
Figure 3-7. With an SSH tunnel in place, your otherwise insecure conversation stays private
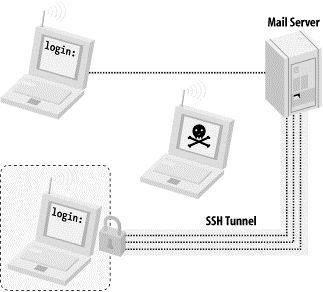
With the tunnel in place, anyone who tries to monitor the conversation between your laptop and the mail server gets something resembling line noise. It's a good idea to get in the habit of tunneling anything that you want to keep private, even over wired networks. SSH tunneling doesn't have to stop at POP connections either. Any TCP port (SMTP, for example) can easily be set up to tunnel to another machine running SSH, almost anywhere on the Internet. We'll see an example of how to do that in Chapter 7. For a full discussion of the ins and outs of this very flexible (and freely available) tool, I highly recommend O'Reilly's SSH: The Definitive Guide, by Daniel J. Barrett and Richard E. Silverman.